In This Article
If you're gearing up for FedRAMP 20x and wondering how many policy documents you need to start writing, you might want to sit down for this one.
FedRAMP 20x doesn't care about your written policies.
That's right. Unlike what you may be used to with FedRAMP Rev 5 or CMMC, the 20x framework shifts the focus away from what you say you do toward what you actually do.
The Old Way of Policies & Procedures
Written policies are a cornerstone of the authorization process for frameworks like Rev 5 and CMMC. These docs are meant to serve as proof of your org’s security.
Businesses spend significant time and resources crafting detailed Word documents (change management policies, access control policies, incident response plans) and these documents serve as key evidence that your organization is "ready" for authorization.
For many organizations, the cost of this process runs well into six figures, with much of that budget going toward manual documentation efforts.
The problem? Polished policy documents don't always reflect what's happening in practice.
A beautifully formatted change management policy doesn't mean much if your team routinely bypasses the process it describes.
Policies Under FedRAMP 20x: Evidence Over Documentation
FedRAMP 20x asks "Can you prove this is actually happening?" Instead of asking "Do you have a policy for this?"
The focus on continuous evidence shows that your security controls are in place and functioning in your environment.
This is part of a broader shift from traditional NIST controls to Key Security Indicators (KSIs), which prioritize measurable, verifiable outcomes over written procedures.
20x Policies in Practice
Let's use change management as an example. Under the old model, you'd draft a change management policy, distribute it to all employees, and present it during your assessment.
Under 20x, your time is better spent:
- Building security controls directly into your CI/CD pipeline so that every new version of your application automatically follows your change management process
- Generating evidence automatically every time a deployment occurs, showing that the controls were enforced
- Demonstrating continuous compliance rather than point-in-time documentation
This is a practical shift, not just a philosophical one. Instead of investing hours polishing policy documents, invest that time in automation that produces real, verifiable evidence.
→ Request a demo to see how Paramify got FedRAMP 20x Low and Moderate Certified and helped many others do the same in just months at a fraction of the traditional cost.
Is FedRAMP 20x Right for You?
If you're a cloud-native SaaS company, this new path could be a game-changer. FedRAMP 20x offers better security, faster authorization without an agency sponsor. If you're already SOC 2 Type 2 compliant, you likely have about 70% of the controls already in place for 20x Low.
Wondering whether the effort is worth it? Get the pros and cons of 20x to decide if it's best for you.
What FedRAMP 20x Policies & Procedures Changes Mean For Your Business
FedRAMP 20x cares about the evidence that shows your security controls are actually in place.
The organizations that will thrive under 20x are the ones that move from a documentation-first mindset to an evidence-first mindset, automating evidence gathering and embedding security controls directly into their operational workflows.
Ready to get started? Check out our step-by-step guide to FedRAMP 20x, or learn more about how Paramify's platform automates the compliance process so you can focus on building your product, not writing policy documents.
Frequently Asked Questions
Do you need written policies for FedRAMP 20x?
FedRAMP 20x does not require the written policy documents that FedRAMP Rev 5 and CMMC rely on. The framework replaces them with Key Security Indicators (KSIs) — verifiable, automated evidence that security controls are actually functioning.
Some lightweight documentation is still expected for specific requirements like change management procedures and ongoing authorization plans, but these are working guides, not formal policy binders.
What are Key Security Indicators (KSIs) in FedRAMP 20x?
Key Security Indicators are FedRAMP 20x's replacement for traditional NIST control-based requirements. Instead of asking whether you have a policy, KSIs ask whether you can prove the control is working — through automated, continuous evidence.
There are KSIs covering areas like change management, vulnerability detection, access control, and supply chain risk. They prioritize measurable outcomes over written procedures.
What is the difference between FedRAMP 20x and Rev 5 policy requirements?
FedRAMP Rev 5 treats written policies — access control policies, incident response plans, change management procedures — as primary evidence of compliance.
FedRAMP 20x treats them as largely irrelevant and focuses instead on continuous, automated evidence that controls are operational. None of the Rev 5 SSP appendices are required under 20x.
What documentation does FedRAMP 20x actually require?
FedRAMP 20x requires documented plans for specific areas: cloud service offering identification (FRR-MAS-01), public information and detailed service lists (FRR-ADS-01, FRR-ADS-03), ongoing authorization reporting (FRR-CCM-01), and top-level administrative accounts guidance (FRR-RSC-01).
These should be concise and practical — think one-pagers, not compliance binders.
What evidence does FedRAMP 20x accept instead of written policies?
FedRAMP 20x accepts automated, continuous evidence that security controls are in place and functioning.
Examples include pipeline logs, automated vulnerability scan results, access control audit logs, and configuration data from your cloud environment.
The goal is evidence generated automatically as a byproduct of how your systems work instead of evidence produced manually for an audit.
Can I reuse my existing FedRAMP Rev 5 policies for FedRAMP 20x?
Your existing Rev 5 policies won't satisfy 20x requirements on their own, because 20x doesn't accept written policies as primary evidence.
But, the underlying operational controls those policies describe are exactly what 20x is looking for, so long as it’s what you’re actually doing. Because of this, organizations with mature security operations often have a shorter path to 20x than they expect.
How does SOC 2 Type 2 compliance help with FedRAMP 20x?
If you're SOC 2 Type 2 compliant, you likely have around 70% of the FedRAMP 20x Low controls already in place. SOC 2 already emphasizes continuous monitoring and evidence-based compliance, which aligns closely with 20x's KSI model.
The remaining gap is typically around government-specific requirements and a few FedRAMP-specific documentation areas.
How long does FedRAMP 20x authorization take?
Many cloud-native SaaS companies are completing FedRAMP 20x authorization in under 30 days. One Paramify client completed the process in two weeks with Paramify.
Your timeline varies depending on how mature your existing security controls are.
How does Paramify help with FedRAMP 20x requirements?
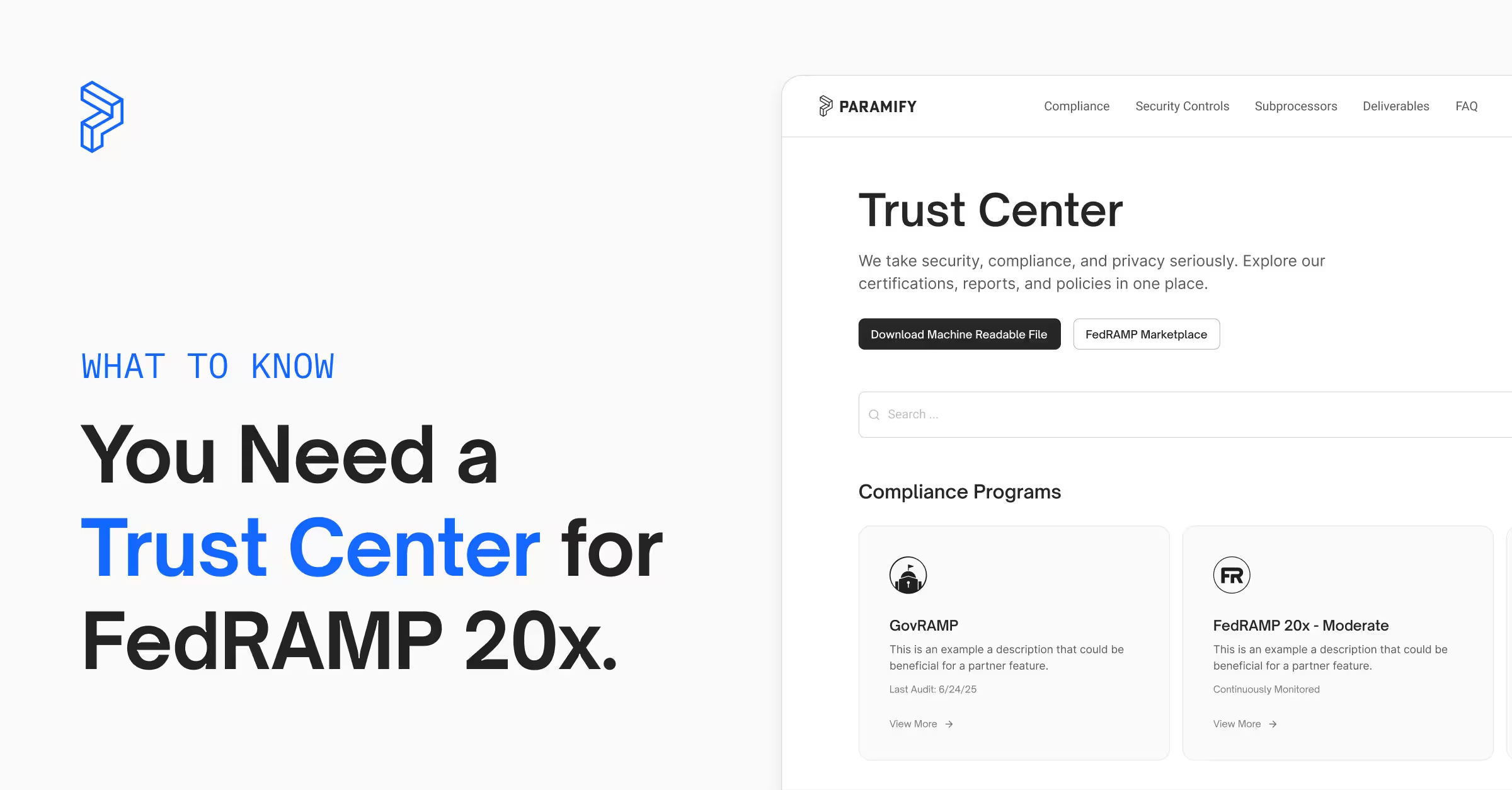
Paramify automates the evidence-based work that FedRAMP 20x actually cares about — mapping controls to KSIs, automating evidence collection for continuous proof of compliance, Trust Center automation, and tracking authorization posture over time.
For areas where lightweight documentation is still required, Paramify helps you build those tied directly to what your systems are doing.
The result: authorization in weeks, not months, without a policy-writing marathon.
Does Paramify generate FedRAMP 20x policy documents?
Where lightweight documentation is still needed, Paramify helps you build it tied directly to what your systems are actually doing — not aspirational prose about what you plan to do someday. We help map KSIs, automate machine-readable documentation, and generate your trust center.