In This Article
FedRAMP is changing — and if you're in the middle of a Rev 5 certification, evaluating your first ATO path, or just tired of hearing "20x is coming" without a straight answer about what that means for you, this is the article you've been looking for.
FedRAMP 20x isn't a renaming. It's a fundamentally different model for how cloud services demonstrate and maintain security compliance. Whether it's right for your organization right now depends on your team, your market, your existing ATO status, and a few honest questions nobody in this space usually answers directly.
We'll answer them here.
Full disclosure upfront: we're Paramify, and we sell a GRC platform that supports both FedRAMP Rev 5 and FedRAMP 20x. We've been deeply involved with 20x and are the first tool to achieve Moderate Certification with 20x. We've seen the differences of both models, so we'll be fully open with you here so you can make the best decision for your business.
What's the Actual Difference Between FedRAMP Rev 5 and FedRAMP 20x?
Basically:
- Rev 5 is response-focused — you document what you do.
- 20x is evidence-focused — you continuously prove what you do.
Rev 5 vs 20x at a glance:
What's the difference between documentation vs Continuous Assessment for FedRAMP
Rev 5 Documentation
The FedRAMP Rev 5 process requires you to
- Map your environment to hundreds of NIST 800-53 controls
- Build out a 1,500+ page System Security Plan (SSP)
- Find an agency sponsor
- Hire a 3PAO for assessment
The Rev 5 process is heavily documentation-driven with auditors spending significant time reviewing and screen-capturing evidence. This means, most of your FedRAMP budget goes to documentation and external consultants and assessors.
20x Continuous Assessment
FedRAMP 20x starts from a different premise entirely.
- Instead of hundreds of controls, you show compliance using Key Security Indicators (KSIs).
- Instead of an SSP, you produce machine-readable documentation and a live, public-facing Trust Center where automated validation pipelines prove your controls are working continuously.
How much does Rev 5 vs 20x cost
The bulk of your FedRAMP Rev 5 spend goes to documentation, and external assessment.
With 20x, assessment costs drop, but you invest more in building and maintaining your own continuous monitoring infrastructure. You're not necessarily spending less; you're spending differently.
More of the budget stays inside your organization, building capability that actually improves your security posture rather than paying for a compliance snapshot.
Do I need an agency sponsor for FedRAMP
20x doesn't require an agency sponsor, Rev 5 does.
If you've been through Rev 5, you know how real that bottleneck is.
An unresponsive agency, a slow sponsor, a bureaucratic stall — any of it can freeze your authorization for months.
With 20x, that external dependency is gone. Go through the process correctly, and you will get authorized. Nothing external can stop you.
Why Choose FedRAMP 20x?
You can get FedRAMP without an agency sponsor
You don’t have to depend on finding the right agency to get 20x Authorization. You can get Moderate Authorized before you find a government buyer. We know it works, because we did it too.
20x Helps you prepare for future FedRAMP requirements
20x is clearly the direction FedRAMP is heading. FedRAMP is already rolling some 20x requirements into Rev 5 offerings with RFCs for
If you're doing Rev 5 today, some of these requirements are coming for you whether you pursue 20x or not. Teams that understand the 20x model ahead of time aren't scrambling when Rev 5 adds another requirement; they've already built for it.

EXAMPLE: FedRAMP now tracks how quickly authorized services respond to communications. If your team doesn't know to monitor response times and act on them, you can get penalized — not because you have a security gap, but because you didn't know the rule existed. Getting your team 20x-aware early prevents exactly that kind of accidental penalty.
20x allows for flexible security
Rev 5 tells you how to meet requirements. 20x says: show what you actually do and allows you to bring what you do best to the table.
If your security practice is genuinely strong in certain areas — custom monitoring pipelines, mature incident response, rigorous vulnerability management — you get credit for the real work you've already done rather than rebuilding it in a FedRAMP-prescribed format.
Government agencies accept FedRAMP 20x
Government agencies are already accepting 20x ATOs. Early signals from the federal community show agencies are excited about the Trust Center model with real-time visibility into a service's security posture, rather than requesting a static SSP and hoping it's current.
That enthusiasm matters when you're trying to close government deals.
You are cloud native
20x is an ideal option if you're built in the cloud — the certification process is simpler and easier.
You can get FedRAMP much faster
If you're evaluating your first FedRAMP authorization path from scratch: 20x is faster.
- The assessment and PMO review cycle is significantly shorter than Rev 5.
- Simple environments can be done in weeks.
- Even complex, multi-stack environments move faster through 20x than through the traditional Rev 5 gauntlet.
Reasons NOT to Choose FedRAMP 20x
You need a DoD ATO
If DoD is your primary market, 20x isn't your path yet.
DoD is not accepting the FedRAMP 20x KSI-based process. We expect that to change, but if IL-4, IL-5, or IL-6 is your near-term target, stick with the traditional path for now.
If this is the case for you, Paramify still significantly simplifies your DoD ATO process and automates your documentation while prepping your program for changes ahead.
You’re not ready for the tech shift
20x will be painful without the right technical resources.
You can expect a shift from GRC admins who own the compliance paperwork to GRC engineers who can build and maintain automation pipelines.
Your 20x process will stall if headcount, skill sets, or deeply entrenched organizational silos between compliance and DevSecOps keep you from bridging that gap.
No platform, including Paramify, fixes that for you. You have to make those teams work together.
You don’t have a GRC automation tool (or plans to get one)
No GRC tool that can support 20x? You'll struggle.
FedRAMP expects most 20x authorized services to use a tool to manage the data and create the trust center.
Trying to homebuild that infrastructure isn't impossible, but it's a significant investment. Home-built solutions also tend to have the traceability gaps that the 20x model is designed to surface.
You think doing Rev 5 manually is a-okay
If you're satisfied with your existing Rev 5 ATO right now, there's no rush to change.
"Satisfied for now" does come with an expiration date, though. Changes are coming to Rev 5. Transitioning to automated processes will only become more difficult the longer you wait to get familiar with the 20x requirements.
The question isn't whether you'll deal with this — it's whether you deal with it on your own timeline or on FedRAMP's.
You're not cloud native
If you have a physical data center that you manage as part of your system, or other non cloud native attributes, Rev 5 may be a better option for you, at least for now.
You think 20x is easy
20x is not an easy button or a pass on actual security.
You cannot fake FedRAMP. You’ll have to constantly prove your security measures up with 20x. These security processes and technical efforts cost money.
But, 20x doesn’t waste money on writing insanely long documents, or audits that blow out the budget. The effort and money you’ll need to spend goes directly into making your security genuinely great.
Can You Do Rev 5 and FedRAMP 20x at the Same Time?
Yes. And, for many organizations, this is the smartest play.
Where do Rev 5 and 20x overlap?
Rather than duplicating effort, you're getting compounding return on a single investment when you do both at the same time.
- KSI evidence from your 20x continuous monitoring program can directly reduce your Rev 5 audit burden.
- You're using the same system boundary, the same automation infrastructure, the same underlying documentation.
20x Trickledown Preparation
The timeline upside is real too. Doing both in parallel means you're not blocked by PMO review cycles or agency timelines to start building 20x readiness.
You move at your own pace, and you're ahead of the curve when the Rev 5 requirements continue shifting in the 20x direction.
Paramify Rev 5 + 20x Case Study
We've taken this approach ourselves at Paramify. We were FedRAMP High Ready and built our 20x program in the same environment. Using the same boundary and the same system meant far less redundant work.
When using Paramify, you pay one price and get both a Rev 5 workspace and a 20x space that mirrors it. Both include automated planning and reporting in whichever format you need (OSCAL and human-readable).
You can generate any required deliverables for either framework from the same underlying work you've already done. And if you're not yet sure which path you need, just start — your Paramify price is the same whether you end up doing Rev 5 or 20x.
What FedRAMP 20x Requires (Where Most Teams Get Surprised)
Understanding the 20x philosophy is one thing. Knowing what needs to be done for it is another. Here’s what you need to know so your team doesn’t get surprised mid-process.
Automation is non-negotiable
20x requires machine-readable evidence. You need automated fetcher scripts pulling proof from your infrastructure in real time.
Paramify provides open-source integrations for the tools we support, and anything we have, we share at no charge.
But if you're running something we don't yet have scripts for — a niche SIEM, a custom logging pipeline, etc — you'll need to figure out how to pull that evidence yourself.
That's real engineering work, and it's yours to own.
Your internal processes are yours to manage
FedRAMP email response SLAs, incident response workflows, SCR processes — no tool automates your organizational discipline for you.
The 20x model gives you more flexibility in how you meet requirements, but the requirements still exist. Build those internal habits early.
Make sure your 3PAO is 20x-ready
Not all 3PAOs have done 20x assessments. Ask directly.
Paramify partners with 3PAOs who are familiar with 20x, and we're happy to connect you with the right fit or sit in on a call to verify readiness if you're not sure about yours.
Your bridge between compliance & DevSecOps has to be built internally
FedRAMP compliance has historically been owned by the paper-chase people — the GRC and compliance professionals who know the framework cold but haven't touched a CI/CD pipeline.
20x requires those two worlds to actually work together. That organizational change comes from inside. No vendor can do it for you.
The sooner you start building that relationship between your compliance team and your engineering team, the smoother your 20x journey will be.
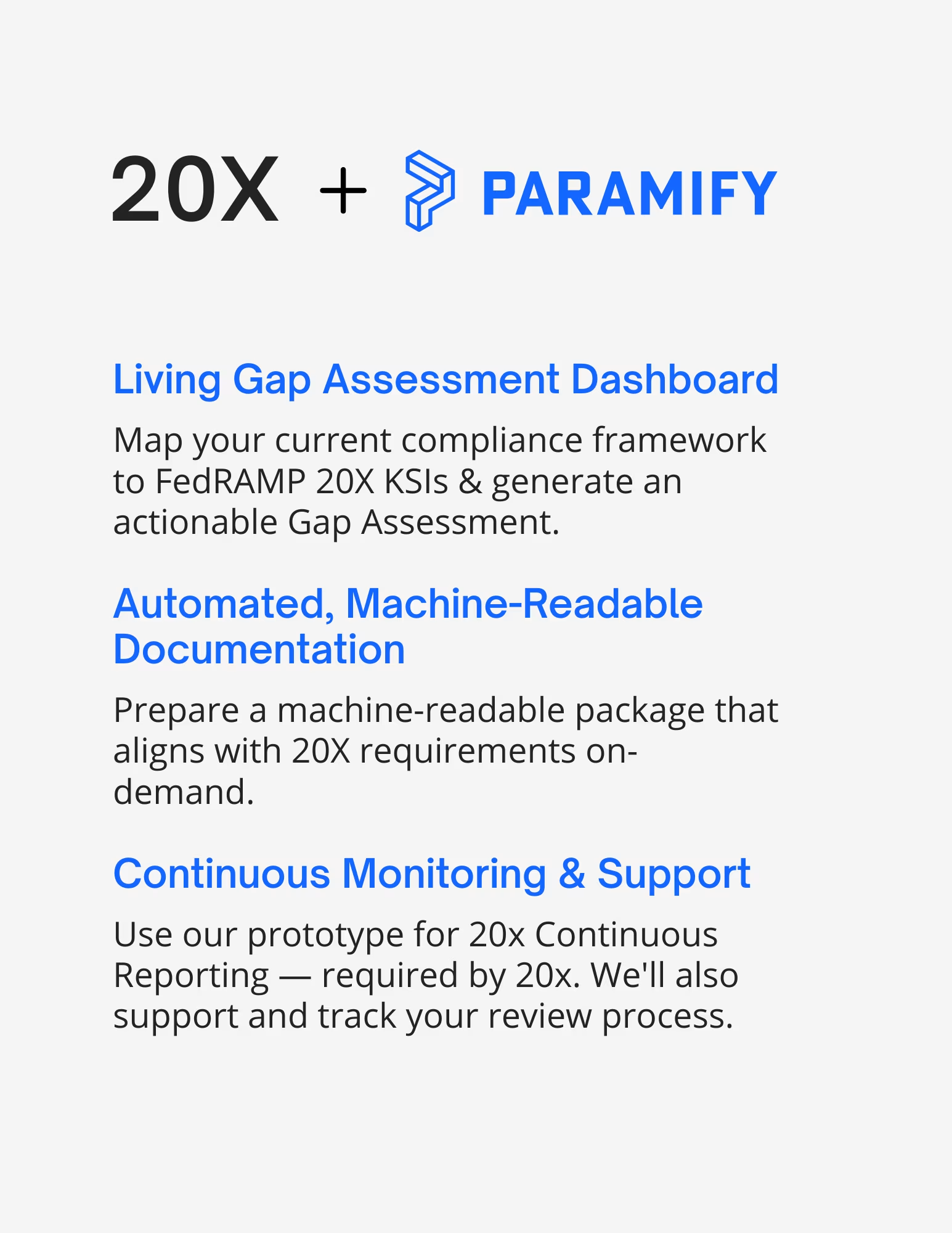
How Paramify Supports 20x
We've helped several businesses with 20x and successfully achieved 20x Low and Moderate ourselves.
The people reviewing 20x packages know our approach and that familiarity matters when it's time for PMO review.
Here's where Paramify makes the biggest differences for 20x:
Machine-readable outputs and Trust Center
FedRAMP 20x runs on OSCAL-native documentation and live Trust Centers. Paramify generates both natively, giving agencies real-time visibility into your posture.
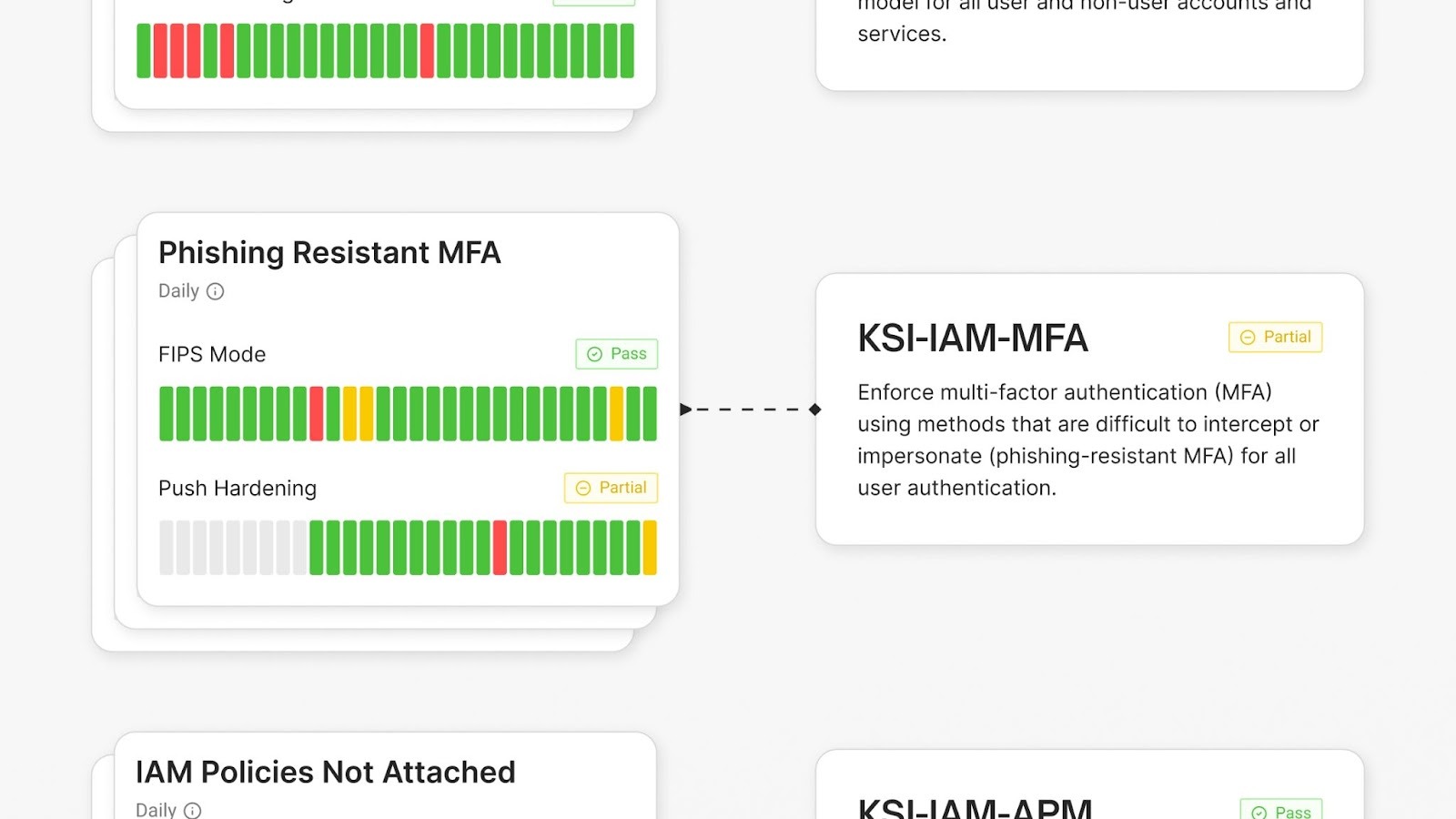
KSI mapping
We map your work to Key Security Indicators automatically. You're not doing that manually and hoping you got it right.
Continuous assessment management
Paramify tracks what's passing, what's failing, and gives you a clear path to meet requirements — not just a dashboard that tells you something's broken with no guidance on what to do next.
Persistent Validation Standard (PVS) traceability
Every party in the 20x ecosystem needs to see a complete, transparent pipeline showing how evidence passes or fails. Paramify provides that end-to-end traceability.
While other tools , and most home-built solutions, leave gaps here. Agencies can see exactly how your controls are being validated, from evidence source to status with Paramify. Nothing is hidden.
VDR (Vulnerability Disclosure and Response) support
20x requires automated detection, response, and reporting on vulnerabilities. Paramify gives you the mechanism to report issues to your agency within the same platform everything else lives in — which FedRAMP specifically appreciates because it keeps the full picture in one place for agency review.
Keep in Mind: Paramify doesn't replace your advisor
Even with Paramify, you may still need a knowledgeable compliance advisor for 20x. If you need strategic guidance navigating 20x, that expertise is worth having separately.
We work closely with top advisors and would be happy to help you find a good match for your goals.
If you’re already using an advisor that isn’t one of our partners, we’d be happy to talk with them and walk them through the platform so you can keep your advisor and enjoy the benefits of Paramify.
→ How to know if you need a FedRAMP Advisor
The Decision Breakdown: FedRAMP Rev 5 vs 20x
Choose FedRAMP 20x if:
- Your primary customers are civilian federal agencies (not DoD)
- You don’t have an agency sponsor
- You have (or can build) the technical resources for automation
- Faster time to ATO matters to your business
- You want to get ahead of where Rev 5 is heading
- You have or are ready to invest in a GRC tool that supports 20x
- You’d rather spend toward security than documentation and audit
Stick with FedRAMP Rev 5 if:
- DoD is your primary market right now
- Your team is non-technical and you can't realistically close that gap near-term
- You have an active ATO you're maintaining and aren't ready to change your program yet
- You haven’t picked a tool to support 20x
Do both in parallel if:
- You have an active Rev 5 ATO and want to future-proof your program
- You want to reduce long-term audit costs by leveraging 20x continuous monitoring evidence
- You want maximum flexibility as FedRAMP continues to evolve and modernize toward 20x processes
The Bottom Line
20x is clearly the path forward if you're targeting civilian agencies, have technical resources, and are willing to invest in automation. If DoD is your market or your team isn't ready for the engineering shift, Rev 5 is where you operate for now — just with eyes open to what's coming.
For most organizations with existing Rev 5 programs, the cleanest path is doing both in parallel: use your existing authorization as the foundation, build 20x readiness alongside it, and let the compounding efficiency pay off over time. You're investing in your own infrastructure rather than someone else's consulting fees, and that investment doesn't expire when the audit ends.
If you want to walk through where your team and tooling actually stand for 20x readiness, we're happy to do that with you.
→ Schedule a demo with Paramify below or request a video demo to see how we support both FedRAMP Rev 5 and 20x from a single workspace for whichever path you need.
Learn More:
→ How Long Does FedRAMP 20x Take?
Frequently Asked Questions
What are the main differences between FedRAMP Rev 5 and FedRAMP 20x?
FedRAMP Rev 5 uses NIST 800-53 controls, requires an SSP, and depends on an agency sponsor.
FedRAMP 20x uses Key Security Indicators (KSIs), replaces the SSP with machine-readable documentation and a live Trust Center, and removes the agency sponsor requirement.
The fundamental shift is from documentation-heavy compliance to automated, continuously validated evidence.
Is FedRAMP 20x faster to achieve than Rev 5?
Generally, yes — significantly faster.
The 20x assessment and PMO review process is designed to be much shorter than Rev 5. Organizations with simple environments can complete it in weeks.
Complex multi-stack environments take longer, but even they move faster through 20x than through a traditional Rev 5 authorization, as long as you have the automation and tooling in place to support it.
Does DoD accept FedRAMP 20x authorizations?
Not yet. As of early 2026. DoD has not accepted FedRAMP 20x.
If your primary target market is DoD Rev 5 remains the required path for now.
Do you need a GRC tool for FedRAMP 20x?
Yes. FedRAMP 20x requires machine-readable documentation, automated evidence pipelines, and a live Trust Center. FedRAMP is actively prioritizing GRC platforms like Paramify in early 20x phases because tooling is what makes the model work at scale.
Attempting it without purpose-built tooling is technically possible, but the manual overhead and traceability gaps make it very difficult to sustain.
Can you pursue FedRAMP Rev 5 and 20x simultaneously?
Yes, and it's often the most efficient path for organizations that already have a Rev 5 ATO.
Work done for 20x (especially KSI evidence and continuous monitoring infrastructure) directly reduces Rev 5 audit burden. You're not duplicating effort when both programs run from the same system boundary and tooling.
Heading 1
Heading 2
Heading 3
Heading 4
Heading 5
Heading 6
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur.
Block quote
Ordered list
- Item 1
- Item 2
- Item 3
- Item A
- Item B
- Item C
Bold text
Emphasis
Superscript
Subscript