In This Article
.avif)
A lot of people are curious how the new FedRAMP 20X KSIs relate to NIST control families (NIST 800-53, NIST 800-171, etc).
FedRAMP 20x is meant to simplify federal cybersecurity compliance. But, since KSIs aren’t directly tied to NIST controls, some worry that it will add extra work and control mappings.
Let’s set your mind at ease. Here we’ll explain what a KSI is, break down the differences between a KSI and control, and show where there are differences between the 20x KSIs and NIST families, so you can know what to expect moving forward
What is a KSI?
A KSI is a Key Security Indicator. This is a measurable metric or control used to assess the security posture of cloud services in FedRAMP.
KSIs are designed to provide a standardized, machine-readable, way to evaluate and monitor the security of a CSPs by focusing on critical security controls or outcomes.
How is a KSI Different from a Control?
Traditional NIST 800-53 controls can be complex and broad. KSIs aim to simplify and streamline security assessments by targeting specific, high-impact security indicators that are easier to automate and validate.
KSIs are part of FedRAMP’s modernization efforts to make security assessments more efficient, scalable, and cloud-native.
They focus on measurable outcomes (e.g., system uptime, patch management compliance, or incident response times) rather than prescriptive processes to give CSPs more flexibility in how they demonstrate compliance.
20x KSIs vs 104 selected 800-53 controls
The FedRAMP PMO has made it clear that the 20x KSIs will not just be an abstraction layer on top of NIST 800 controls.
KSIs are meant to show capabilities and provide flexibility for CSPs.
But, KSIs also have “related controls” that show how they may relate to NIST controls.
It can be a useful exercise to compare the current FedRAMP Low baseline requirements (NIST 800-53 selected controls) to the 20x KSI “related controls” to see what the focus of 20x requirements are from a NIST control lens.
When we dig into the related controls a few key insights emerge.
NIST 800-53 Rev 5 Controls Excluded from FedRAMP 20X
Which NIST 800-53 Rev 5 Controls for FedRAMP Low are excluded from the FedRAMP 20x KSI “related controls”?
Learn more: CISA Secure Software Development Attestation Form
Which NIST 800-53 Rev 5 Controls that are 20x KSI “related controls” are added to existing FedRAMP Low controls?
What Fewer KSIs Means for Your Security Program
KSIs are reducing and simplifying the control set for FedRAMP.
There are a lot more controls removed than added (as you can see above).
Some NIST control families like Maintenance (MA), Media Protection (MP), and Physical and Environmental Protection (PE) which are included in the FedRAMP Low Baseline, are completely excluded from 20x KSIs.
This is good news for CSPs and it’s possible because the KSIs are Cloud Native. A cloud service offering will already inherit most controls in these families from their LaaS providers (AWS, Azure, GCP, etc).
The change to KSIs is meant to give you flexibility that wasn’t possible with the required detail and rigidity of NIST controls.
KSIs are Simple With Risk-Based Security
KSIs shouldn’t be seen as a new set of requirements. They are based on NIST FedRAMP baselines but modernized for cloud native offerings and condensed to focus on capabilities.
If you’re concerned about updating your security program, it all boils down to this:
If you do risk management and have secure practices you will be fine.
When you manage risk effectively any control standard will be easy to assess because you have made risk-based decisions to protect your assets, processes and people.
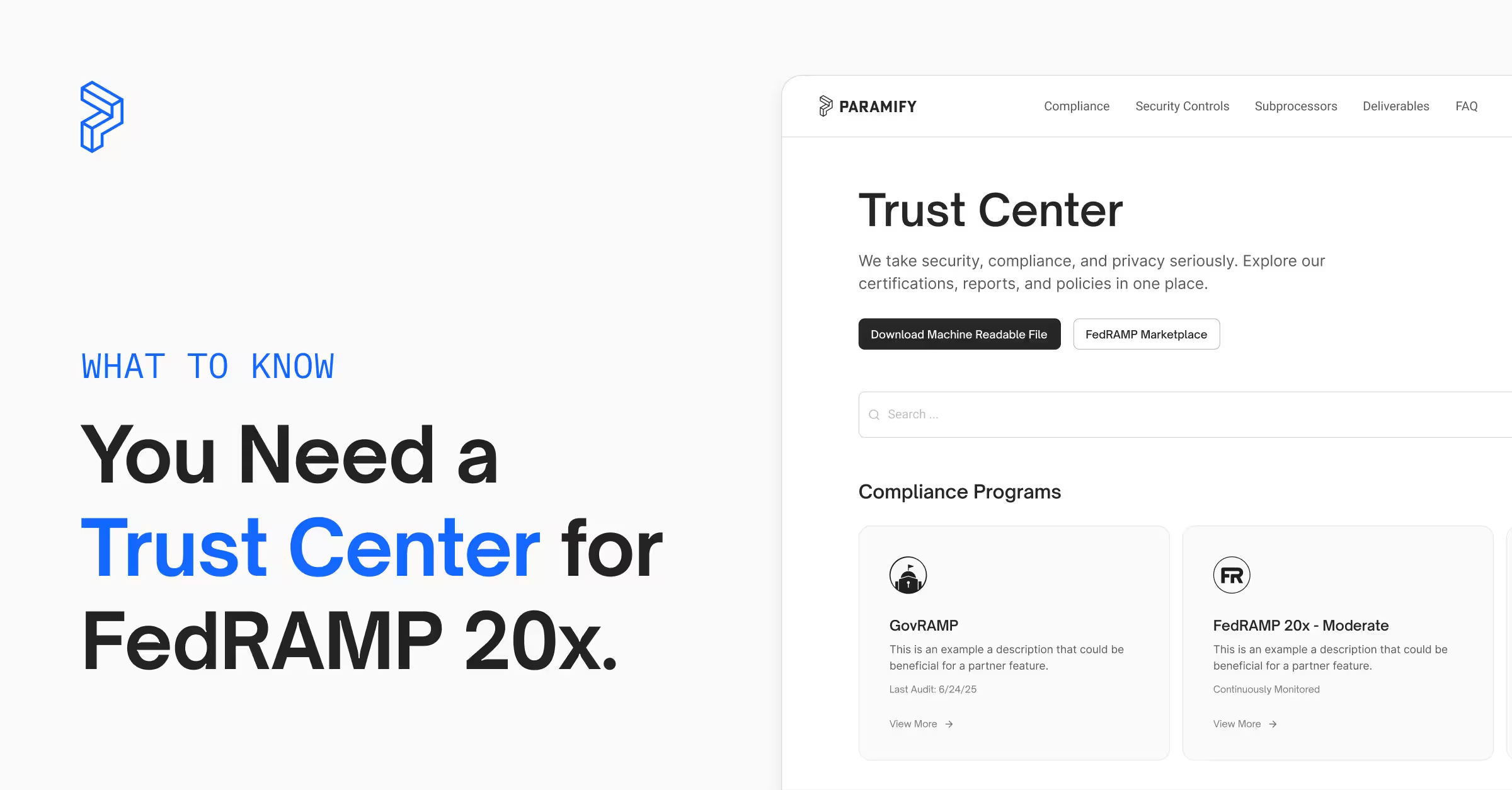
Paramify’s risk solutions focus on managing risk first. We’ve achieved FedRAMP 20x Low and Moderate Authorization to get a first-hand look at what’s changing. We’ll stay up to date on changes, so you can know your security program meets compliance requirements no matter what changes.
Prepare for FedRAMP 20x
Implementing a risk-based security approach is simple when you use Paramify. You can even build the majority of your security strategy in just 45 - 60 minutes.
Have questions? Please reach out — our team loves to help.
Sign up for free demo of Paramify below, or request a demo video, to start preparing for FedRAMP 20X today:
→ Risk-based vs compliance-based security: Here's the difference