In This Article

There’s a new standard in FedRAMP land: the Vulnerability Detection and Response Standard. VDR for short. But, come on, we're calling it Vader. Like Darth Vader, but nerdier and obsessed with enforcing vulnerability management instead of killing Jedis.
Let’s get into what it all means, how VDR is changing ConMon, and when it will affect your organization.
What is the Vulnerability Detection and Response (VDR) Standard?
TL;DR: The FedRAMP VDR standard is meant to keep CSPs on their A-game by automating and continuously proving vulnerabilities are managed.
FedRAMP just dropped the first Vulnerability Detection and Response (VDR) standard—release 25.09A.
This is meant to be a major upgrade to how CSPs hunt, assess, prioritize, patch, and report on vulnerabilities. VDR replaces old-school, scanner-obsessed rules, endless Plan of Actions & Milestones (POA&Ms), inconsistent reporting for something much more modern and automated.
VDR is all about outcomes: Did you actually shrink the risk? Fast? And can you prove it?
It's automated, persistent (using scanners, threat intel, bug bounties, supply chain vibes, and more), risk-driven (factoring in stuff like asset criticality, exploitability, and how reachable it is from the internet), and super transparent to agencies with regular reports and machine-readable data.
FedRAMP is also hinting at future comparative scoring across providers, so you can see how your vuln game stacks up to other CSPs. "Scan and forget” won’t fly in the future. Real risk reduction, especially for those sneaky internet-reachable vulnerabilities, will be required.
Why is VDR Necessary?
POA&M templates have been the standard for tracking vulnerabilities in FedRAMP, but they create major problems — static files, flawed assumptions, and teams constantly 45 days behind reality.
Templates often fail and lead to bad security practices. VDR is designed to fix this. By focusing on real data instead of paperwork, VDR shifts compliance from point-in-time snapshots to continuous readiness. The goal is to bringing agencies and vendors closer to true continuous ATO.
The Three Key Filters for Vulnerability Management
When you're staring down vulnerabilities in your FedRAMP environment, you've got to run them through these three filters. They're like your vulnerability triage system that helps you figure out what's a fire drill and what's just a minor annoyance.
Filter 1: Is It a LEV or NLEV?
LEV is short for Likely Exploitable Vulnerability.
Basically, this is asking if the vulnerability is out there in the wild, totally unmitigated. No protections, no barriers — it's just hanging open, waiting for someone with a reasonable amount of know-how to stroll in and exploit it.
These LEVs could be everywhere or super rare depending on your setup.
The key is knowing your environment inside out from the get-go. If it's mitigated with things like firewalls, patches, whatever, then it's not a LEV.
Simple as that. But if it's exposed? Game on for potential bad actors.
What’s a NLEV? Something that’s a Non-Likely Exploitable Vulnerability. It’s a vulnerability, but not quite so urgent.
Filter 2: IRV or NIRV?
An IRV is an Internet Reachable Vulnerability (a NIRV: NOT an Internet Reachable Vulnerability.)
Sounds straightforward, but people often trip up here.
Folks sometimes think, "Oh, it's behind firewalls, so it's not reachable from the internet." Wrong! This stuff happens all the time, especially with cloud storage. You set something to world-readable by accident, and boom, someone pokes a hole right through your fancy tech stack.
It's like turning your firewalls into Swiss cheese. Even with all the bells and whistles, if it's accessible from the web, it's an IRV.
So, don't assume protection; verify it.
Filter 3: What's the Impact of Your Data?
And finally, the big one that should probably come first in your mind: What's the impact level of the data flowing into your organization? This dictates everything. From the controls you need, to the detection speed, and how fast you have to respond under VDR.
We're talking low, moderate, or high impact systems. Low means lighter timelines for fixes; high means drop everything. It all ties into how sensitive the data is and what VDR requires from you in terms of vulnerability hunting and patching.
Breaking Down the Adverse Impact Ratings: N1 to N5
Let’s get into the potential adverse impact ratings. These are labeled N1 through N5. Now, I'm not sure what the "N" stands for exactly. Number? Negligible? Something clever, I'm betting, because these standards love their acronyms.
But for us practical folks, think of them as priority levels.
Heads up though, organizations often get this backward. In some places, a P1 or, even scarier, P0 means "drop everything, this is panic mode." But it’s flipped here.
The higher the number, the bigger the problem.
Here's a mind-bender: Even if you're a low-impact system, could you still hit catastrophic?
It's unlikely, but it is possible.
If access is down for more than a day or exploitation goes uncontrolled — data theft, unauthorized access galore — it could wreck an agency's operations.
Low impact doesn't mean zero risk; unauthorized folks stealing agency data from your CSP? That's catastrophic territory whatever your impact level.
Remediation Timelines: How Fast Do You Have to Move?
What does all this mean for timelines? It all depends on your system's impact, the filters (LEV/IRV), and that N rating.
For example, these are the timelines for a LEV at N5 for the different impact levels:
- Low-impact system: You've got 4 days to fix it. That's quicker than the old high-impact 30-day window, showing how serious VDR is.
- Moderate impact: 2 days. Right in the middle.
- High impact: Half a day. This is a pants-on-fire, no-sleep-till-it's-done situation.
This is pants-on-fire stuff for a reason. We've dealt with P0 bugs on the functionality side. Mistakes happen, but we treat them like the world-ending events they could be.
Fix fast, no excuses.
VDR aligns with that: Important vulnerabilities get automated responses; the negligible ones? Don't sweat 'em.
Automation Tools Are Your Best Friends for VDR
The only way to stay on top of this? Automation, baby.
The right tools are crucial because you can't manually sift through vulnerabilities and hit these timelines. You’ll need processes that detect, assess, and patch automatically where possible.
In a high-stakes environment, you’ll want systems alerting you to LEVs and IRVs instantly. From there you can prioritize the N5s and automate the fixes for lower ones.
We've had our share of fire drills, but with good automation, things can be well controlled.
These aren't just FedRAMP mandates; they're best practices we should be doing anyway. Focus on what matters, automate the response, and keep your cloud secure without losing sleep over every little thing.
In the end, VDR is here to make us better — faster responses, smarter filters, and a framework that matches real-world risks.
Change is in the air, let's embrace it and level up our vulnerability game.

When Does the New VDR Standard Go Into Effect?
For FedRAMP 20x Pilots:
VDR is effective September 15, 2025 for FedRAMP 20x.
Phase One gives you up to a year post-authorization to fully implement, with quarterly check-ins.
For Phase Two? You’ll want to show big progress before you even get authorized. If you want to do 20x, VDR is knocking on your door now so plan ahead. You’ll want to show you're moving, but perfection isn't required Day 1.
For FedRAMP Rev5:
The earliest the VDR standard could go into effect is October 8, 2025, but that's just for the Closed Beta (R5.VDR.B1).
You’ll need to enroll in the Beta program to get FedRAMP's thumbs-up before tweaking your ConMon.
FedRAMP is eyeing FY26 Q2 for a broader Open Beta, and maybe optional wide release in Q3-Q4, with a potential one-year transition grace period (fingers crossed, based on precedents).
Bottom line:
If you're a Rev5 CSP not in the Closed Beta — no immediate changes. Keep your current ConMon humming, but maybe start piloting VDR-friendly tweaks on the side.
Also checking the stop-slop skill:Here's the blog section:
Do You Need a Separate Threat Intelligence Program for FedRAMP 20x VDR?
Short answer: no. If your scanning tools are modern and pulling from current vulnerability databases, you're almost certainly covered.
This is one of the more common points of confusion in FedRAMP 20x's Vulnerability Disclosure Requirements (VDR), so it's worth unpacking exactly where threat intelligence fits — and where it doesn't.
Detection vs. evaluation: two different jobs
The VDR standard separates vulnerability detection from vulnerability evaluation, and threat data plays a different role in each.
On the detection side, VDR-CSO-DET lists threat intelligence as one of several "appropriate techniques" — alongside scanning, assessments, bug bounties, and supply chain monitoring. That's an and/or list, not a checklist. You're not expected to implement all of them.
Where threat data actually matters is in evaluation. VDR-EVA-EFA factor 8 says you should consider "Known Threats" when contextualizing vulnerabilities you've already found. This isn't about running a separate threat intel program. It's about asking the right questions when you evaluate a finding: Is this being actively exploited? Is there a known exploit in the wild?
What "modern tools" actually covers
If your scanning tooling pulls from CVE/NVD, incorporates EPSS scores, and flags CISA KEVs, you're already meeting the spirit of factor 8. Tools like Wiz, Qualys, Tenable, CrowdStrike, and Grype all bring this context in natively. You likely don't need to bolt anything on.
What FedRAMP actually cares about
FedRAMP has been explicit that they care about outcomes, not specific tooling. The VDR-EVA-ELX notes make this plain: the real test is whether you're evaluating vulnerabilities thoughtfully. Providers who dismiss findings without working through the evaluation factors — exploitability, reachability, adverse impact, known threats — are the ones who get burned come authorization time.
If your tools are doing that evaluation work automatically, and you're tracking and responding to findings within the VDR timeframes, you're in line with the standard. No separate threat intel subscription required.
Prepare Your System for VDR
VDR is here to make us better with faster responses, smarter filters, and a framework that matches real-world risks.
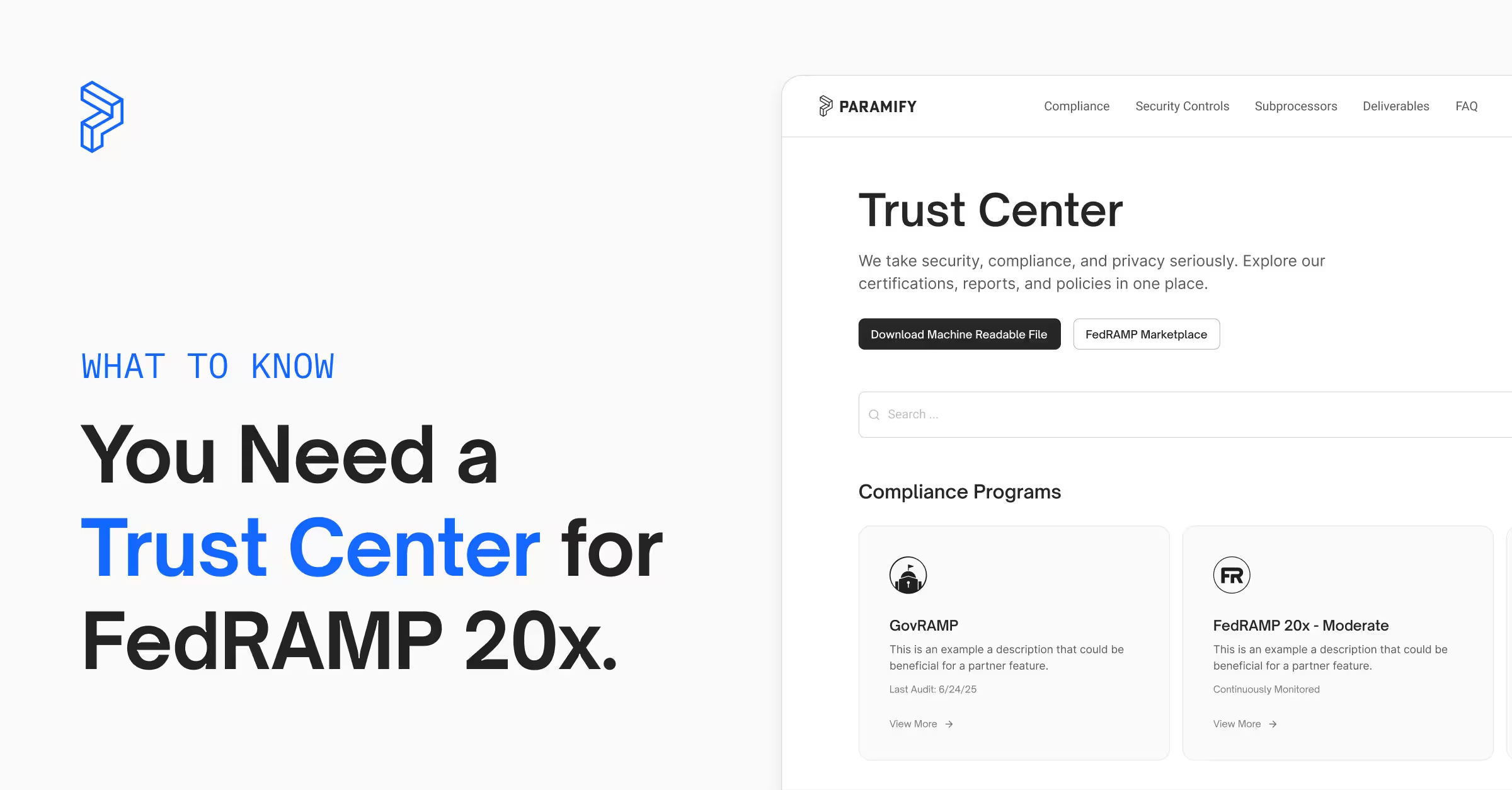
If you’re considering FedRAMP 20x, or looking to automate and prepare for what’s ahead, we’d love to help. Paramify has helped many CSPs get automated fast and we’re confident we could streamline your compliance and ConMon too.
Learn more about what we do, see our pricing, and request a quick demo video or sign up for a live demo below to get started.
Learn More:
Is Paramify Right for Your 20x Transition?