In This Article

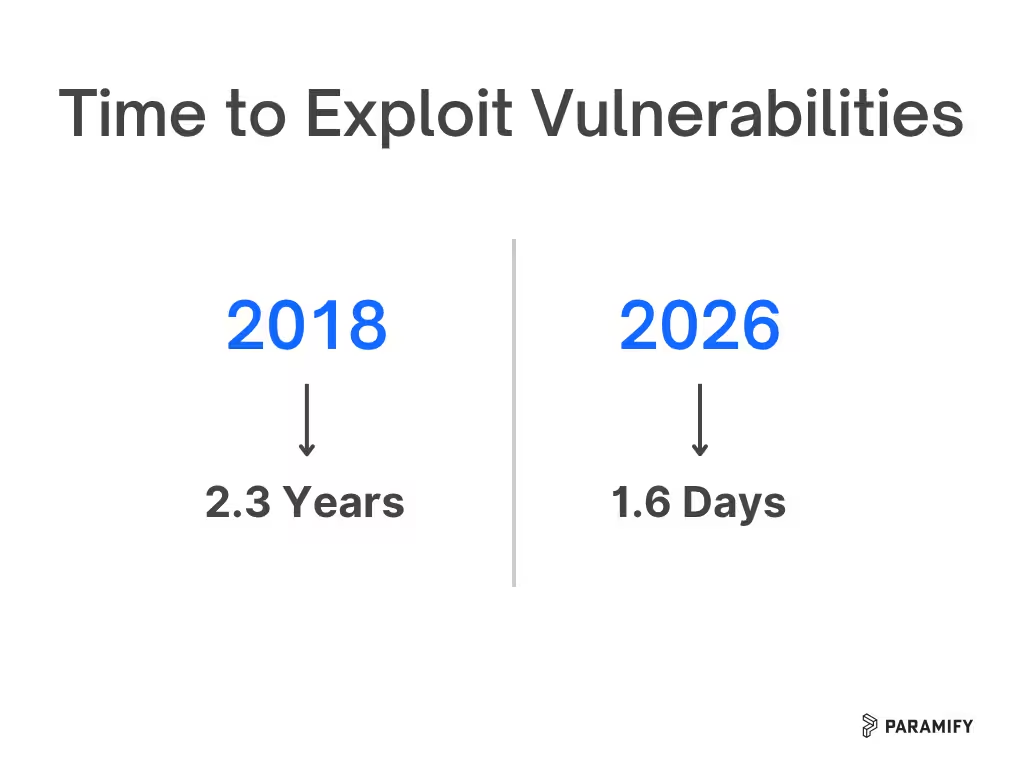
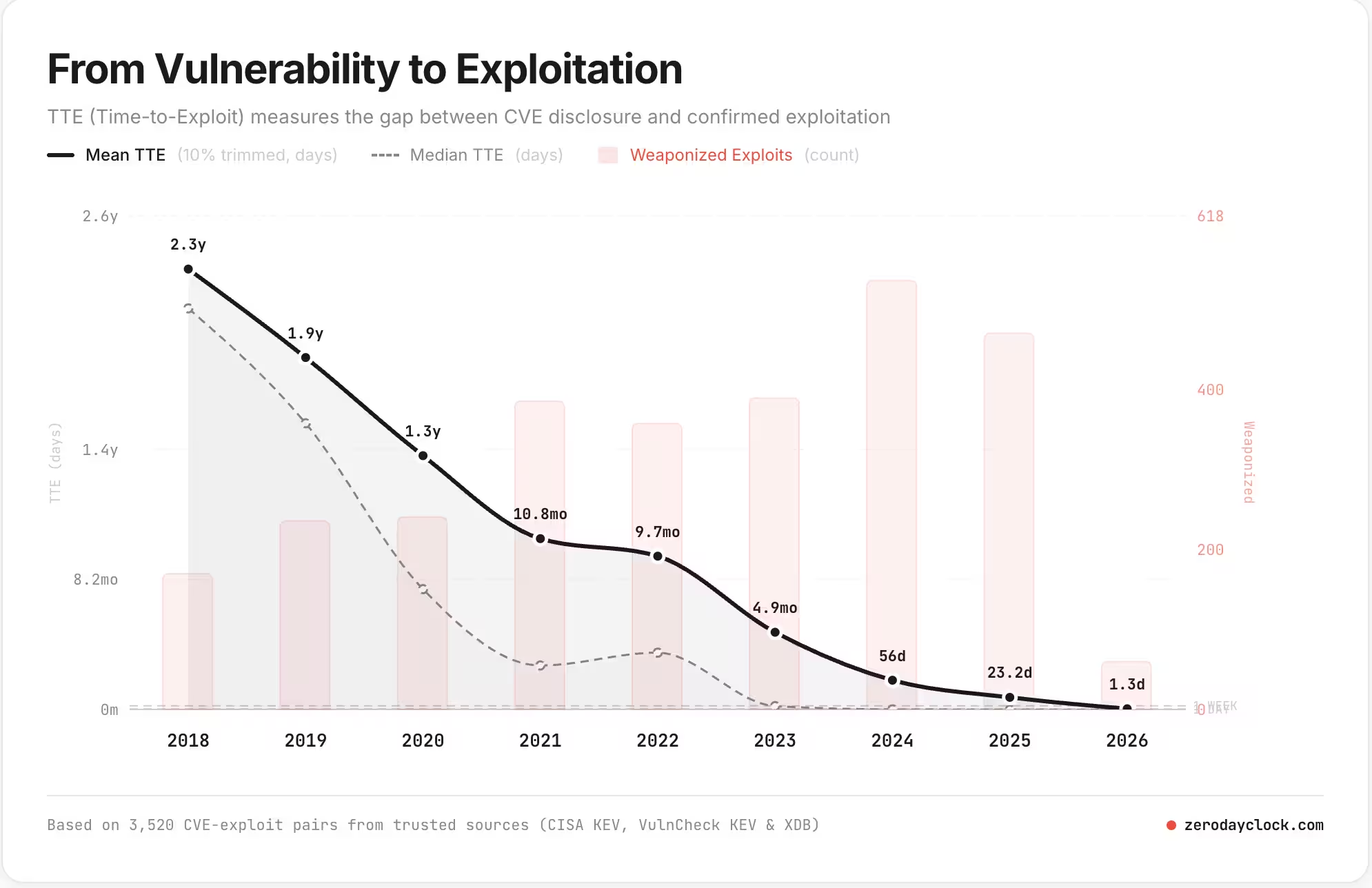
Attackers needed an average of 2.3 years to develop a working exploit if a new vulnerability was published in 2018. That window gave compliance teams breathing room to scan quarterly, update a spreadsheet, and call it a day.
That window is gone. Average time to exploit is now 1.6 days.
AI has made it far easier to write exploit code against known vulnerabilities. Federal compliance programs built around monthly scans and manually updated POA&M spreadsheets weren't designed for this world.
Here's what the data actually shows, why the old FedRAMP vulnerability management process is failing, and how modern teams are managing vulnerabilities better and faster.
Why is Vulnerability Time-To-Exploit Shrinking?
The Zero Day Clock project tracks vulnerability exploitation timelines, and the trend line is not encouraging.
The time-to-exploit metric is the gap between when a CVE is published and when a working exploit appears in the wild. And It has shrunk dramatically over the past several years:
- 2018: Average time to exploit = 2.3 years
- Today: Average time to exploit = 1.6 days
AI is the primary driver of the change. Large language models make it faster and cheaper to analyze a published vulnerability, understand the underlying code flaw, and generate proof-of-concept exploit code.
Attackers only need a good prompt and a few hours to do damage.
This creates a very real problem for FedRAMP companies: If you're only scanning for vulnerabilities monthly, a new critical CVE could be published, weaponized, and actively exploited before your next scan even runs.
The Problem With the Current FedRAMP Vulnerability Process
FedRAMP's traditional vulnerability detection and response workflow was designed for a different threat era. Here’s what the process looks like now:
- Run a vulnerability scan (monthly, maybe quarterly)
- Export the results
- Manually update a POA&M spreadsheet
- Submit that spreadsheet to your agency
When it took years for a vulnerability to become a real exploit, this worked well enough. A monthly cadence meant you'd catch issues with plenty of time to remediate before they mattered.
Now? That process is a liability.
A vulnerability published on a Tuesday morning could have working exploits by Tuesday afternoon. If your next scheduled scan is three weeks away, you have a three-week blind spot. Attackers know how to use it.
This isn't hypothetical risk. It's the operational reality that federal compliance teams are increasingly navigating.
Why Do Vulnerabilities Get Ignored?
The truth: Most vulnerabilities don't actually matter
Here's a fact that surprises a lot of people, the exploit rate — the percentage of all published CVEs that are ever actually exploited in the wild — is extremely low.
Typically around 1.5–2%.
In 2026 so far, roughly 64 CVEs have been confirmed exploited out of the thousands published.
This means that for every 100 vulnerabilities your scanner surfaces, only one or two are likely to ever pose a real risk to your systems. The rest may have no working exploit, require physical access, only affect configurations you don't use, or have never been observed in an actual attack.
This is a critical point that the current FedRAMP process completely ignores. Manual POA&M management treats a theoretical low-severity vulnerability the same as an actively exploited critical one.
While the handful of vulnerabilities that actually get exploited are buried in the noise, teams burn enormous time tracking, documenting, and reporting vulnerabilities that will never be used against them.
The right approach isn't just faster scanning. It's smarter prioritization: identify the vulnerabilities that are actually likely to be exploited in your specific environment, and focus your energy there.
How is FedRAMP 20x Improving the Vulnerability Problem?
FedRAMP 20x is modernizing its vulnerability detection and response standard to address the prioritization problem. They’re moving away from periodic manual processes toward continuous, automated detection with risk-based prioritization.
Basically, compliance programs that are still relying on monthly scans and spreadsheet-based POA&M tracking are increasingly misaligned with where FedRAMP is heading.
→ Get your step-by-step process on How to simplify your 20x process
What Does Modern Vulnerability Management Look Like?
Paramify has worked with a lot of federal compliance teams who've been through this transition. The ones who've gotten it right share a few things in common.
They use automated, continuous scanning tools
Wiz, Qualys, Tenable Nessus, and Burp Suite are excellent scanning options depending on your stack and environment.
Tools like these help you move from periodic snapshots to ongoing visibility. A vulnerability that appears on Monday gets flagged on Monday, not three weeks later.
They prioritize ruthlessly
"Every vulnerability is equally important" is a recipe for burnout and missed critical issues.
Raw scanner output is noisy. Teams who've built (or adopted) a workflow that surfaces the CVEs with active exploits, high EPSS scores, and relevance to their actual environment — and deprioritizes everything else — are the teams that aren’t drowning.
They automate the POA&M workflow
Manually translating scan output into a POA&M spreadsheet, deduplicating findings, and formatting for agency submission is exactly the kind of grinding work that should be handled by software, not people.
Think about it, every hour a compliance analyst spends formatting a spreadsheet is an hour they're not spending on remediation.
How Paramify Fits In
Paramify integrates directly with the major vulnerability scanning tools like Wiz, Qualys, Tenable Nessus, Burp Suite, and others. The workflow is straightforward:
- Export your scan files from whichever scanner you're using
- Upload them to Paramify, which deduplicates CVEs across tools and scan runs so you're working with a clean, consolidated picture
- Focus on what matters — Paramify helps surface the vulnerabilities that are actually relevant and likely to be exploited rather than burying you in thousands of low-signal findings
- Auto-generate your POA&Ms — Paramify creates the POA&M spreadsheet template formatted for federal agency submission, so you're not rebuilding that from scratch every cycle
This results in a vulnerability management process that's fast enough to actually keep pace with 1.6-day exploitation timelines, without 3Xing your team.
→ Request a video demo to see how Paramify cuts down POA&M pain
Automate & Modernize Vulnerability Management
The threat landscape changed. The time to exploit dropped from years to hours. AI made it faster and cheaper to weaponize published vulnerabilities, and it's also helping researchers discover more vulnerabilities in the first place — which means the volume of findings is going up while the time you have to respond is going down.
Monthly scans and manual spreadsheets were never elegant. Now they're genuinely inadequate. The good news is the path forward is clear: automated continuous scanning, intelligent prioritization, and automated POA&M generation.
Federal compliance doesn't have to be the last department to catch up to the threat landscape.
Request a demo to see how Paramify handles vulnerability deduplication and automated POA&M generation, or reach out if you want to talk through your current process.
Frequently Asked Questions
How fast are vulnerabilities being exploited in 2026?
The average time from vulnerability disclosure to active exploitation has dropped to approximately 1.6 days, down from 2.3 years in 2018. AI-assisted exploit development is the primary driver of this acceleration.
What percentage of published CVEs are actually exploited?
Typically around 1.5–2% of all published CVEs have known exploits used in the wild. This means that for every 100 vulnerabilities a scanner surfaces, only one or two are likely to pose a real risk — making prioritization as important as detection speed.
Why are monthly vulnerability scans no longer sufficient for FedRAMP?
When exploits can emerge within hours of a CVE being published, a monthly scan cadence creates weeks-long blind spots where new vulnerabilities could be actively exploited before your team even knows they exist. Continuous or near-continuous scanning is increasingly necessary.
What is FedRAMP 20X doing about vulnerability management?
FedRAMP 20X is updating its vulnerability detection and response standards to move toward continuous, automated scanning and risk-based prioritization — shifting away from the traditional monthly scan and manual POA&M spreadsheet model.
What vulnerability scanners does Paramify integrate with?
Paramify integrates with Wiz, Qualys, Tenable Nessus, Burp Suite, and other leading vulnerability scanning tools. Scan files can be uploaded directly into Paramify for deduplication and automated POA&M generation.